Devilish Joker Android Malware Tricks Its Way Into Google Play Store Yet Again

The billing fraud and SMS-stealing malware known as Joker has returned to the Google Play Store after having its ups and downs dating back to 2017. Researchers now say Joker has a new bag of tricks and can avoid Google’s app-vetting process and sneak onto the market.
Disguised within legitimate-looking apps, Joker can steal text messages, contact lists, and device information and then subscribe users to unwanted paid and premium services. Thankfully, thousands of Android applications infected with Joker have been taken down from the Google Play Store in the past several years, but it does not seem that this was enough.
Since September of 2020, when the last wave of Joker takedowns happened, several things have changed, according to researchers at Zimperium zLabs. Perhaps most concerning is that the threat actors have taken to using legitimate development techniques to blend in, subsequently hiding the payload from security toolsets. Further, “they are starting by using the common framework Flutter to code the application in a way that is commonly seen by traditional scanners.”
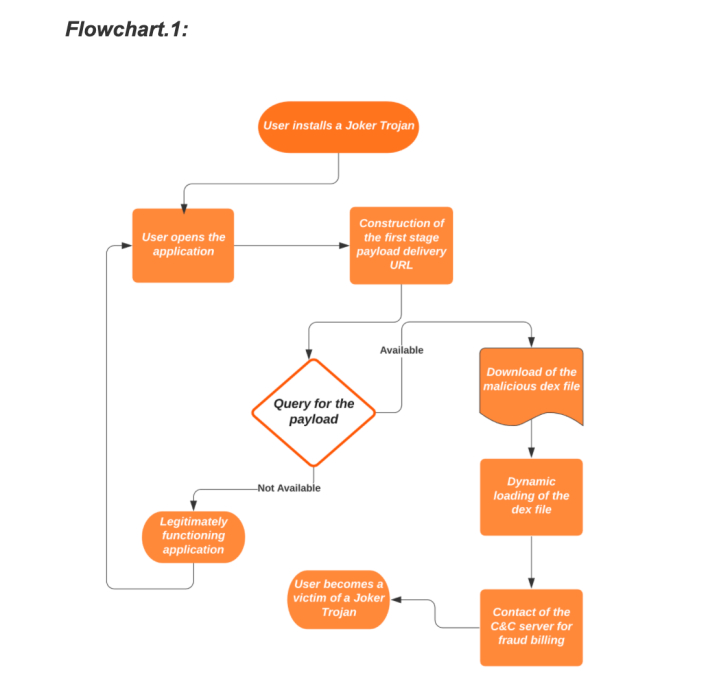
The threat actor could also hide the payload within encrypted .dex files or regular .dex files within images using steganography. Either way, after installation, applications infected with Joker run a scan using Google Play APIs to see if it is the latest version of the app. If it is the latest version of the app or there is no reply, “the malware remains silent since it can be running on a dynamic analysis emulator.”
As it turns out, both consumers and enterprise Google Play users are at risk due to the infected apps sneaking past Google. Of course, it is always good to do due diligence when installing anything, which also goes for apps. Though some apps may look legitimate, anyone can do some background research within the Google Play Store to check reviews, the number of downloads, publish date, and who the publisher is.
If an infected app then gets past that filter, people will have to manually clean their devices. Thankfully, malware like this generally only leads to a short-term financial loss if caught early enough, but it is still something you do not want to deal with.