As you're surfing the web, it is a pretty fair bet that most of the websites you visit run on a Linux-based operating system. It is the world's most popular server platform, after all. Thanks to the open-source nature of
Linux, it is often considered far more secure than most alternatives, as any vulnerabilities usually are patched pretty quickly. And yet, we come to you today with a particularly nasty security issue.
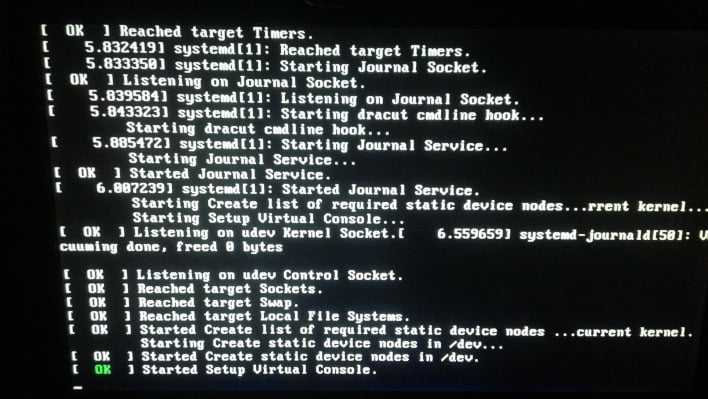
The recently discovered vulnerability is named Dirty Pipe, thanks to a limited similarity to a Linux vulnerability discovered in 2016 called
Dirty Cow. Unlike Dirty Cow, this one utilizes what is known as a pipe operation to exploit the active cache of the operating system. Unfortunately, the cache does not have any particular user-level access lockdowns. Because of this, utilizing this exploit allows the attacker to overwrite immutable or read-only access files that would only be accessible to the kernel operation or root access.
Having that level of unwarranted access to a machine can be extremely nasty. That means that the attacker, with the correct information, would be able to modify drivers, create new users, grant those users root, or just run commands on any user they wish that might not even generate logs. There is more concern—as a kernel-level exploit, any affected Linux operating systems running the versions associated are affected by this vulnerability, which means
Android too.
There is some silver lining, though. The researcher who found this,
Max Kellerman, decided to do the right thing and report this exploit and submitted a patch to the Linux repository and the Android repository before publicizing the exploit itself. Both associated repositories have already accepted the patch and have new kernel versions available.
The problem is primarily in version 5.8, but the patched versions of the kernel are 5.16.11, 5.15.25, and 5.10.102. Another bit of respite for those concerned about security on their servers and Linux systems is that the attacker would already need localized access to the device before the exploit would be effective. Hopefully, the distributors of Linux-based systems can get their kernels patched before too many people exploit it like was done with Dirty Cow.