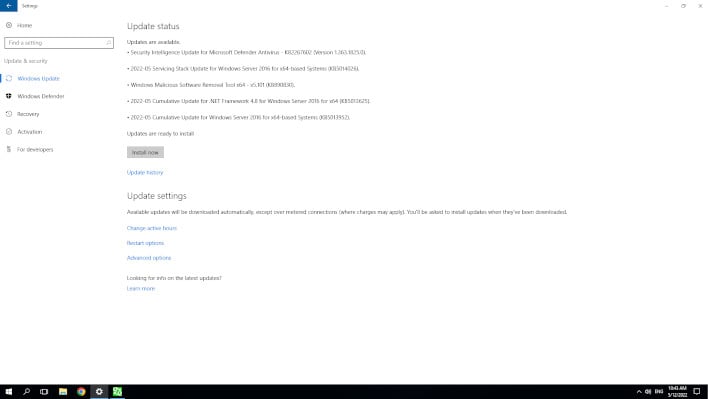
Microsoft Windows Patch Tuesday Update Bug Is Causing Major Authentication Headaches

Specifically, the patch has problems relating to authentication. Unfortunately, it looks like the issue exists on all versions of Windows, including Windows 11 and Server 2022. The knowledge of the issue seemed to have shown up in the r/sysadmin Subreddit, where some users pointed out they received the following error. "Authentication failed due to a user credentials mismatch. Either the user name provided does not map to an existing account or the password was incorrect." Or something similar.
There's some good news and some bad news related to this. The error seems to only affect versions of Windows that are being used as Domain Controllers and those that use Kerberos. That's actually the bad news because that's potentially a lot of servers. That's also the good news, because it means home users are likely unaffected by the issue. The other good news is that Microsoft is already working on a patch.

In these updates, there's been updates to certificate mapping, which has caused some automatic forms of this to fail. Because certificates are key to domain security, there will definitely be some authentication failures. There are some workarounds, as Microsoft itself advises manual mapping of certificates.
Some users state that if dealing with Kerberos, it might be an okay, but not ideal, way to bypass the issue if you find and set the registry key named StrongCertificateBindingEnforcement to 0. According to Microsoft, the Patch actually was turned on by default due to the patch. It is a REG_DWORD Data Type if you wish to take that route, but be aware that this particular action is not advised by Microsoft. You can also just uninstall the patches, but this leaves those critical vulnerabilities exposed on your system.