Questionable AMD PCI Driver May Improve Game Stability But Could Be A Security Headache

We have seen major OEMs tinker with drivers and system settings for workarounds and various fixes in games and other apps before. And now that AMD is firmly back in the mainstream desktop processor race, the company is occasionally under the microscope with power users and developers that stumble onto similar patch type efforts. In that regard, it appears Ryzen systems may pose a potential cause for concern. A researcher has found a seemingly disguised AMD driver toggling certain system behaviors when it detects a list of games, which could open the door to security vulnerabilities and other issues.
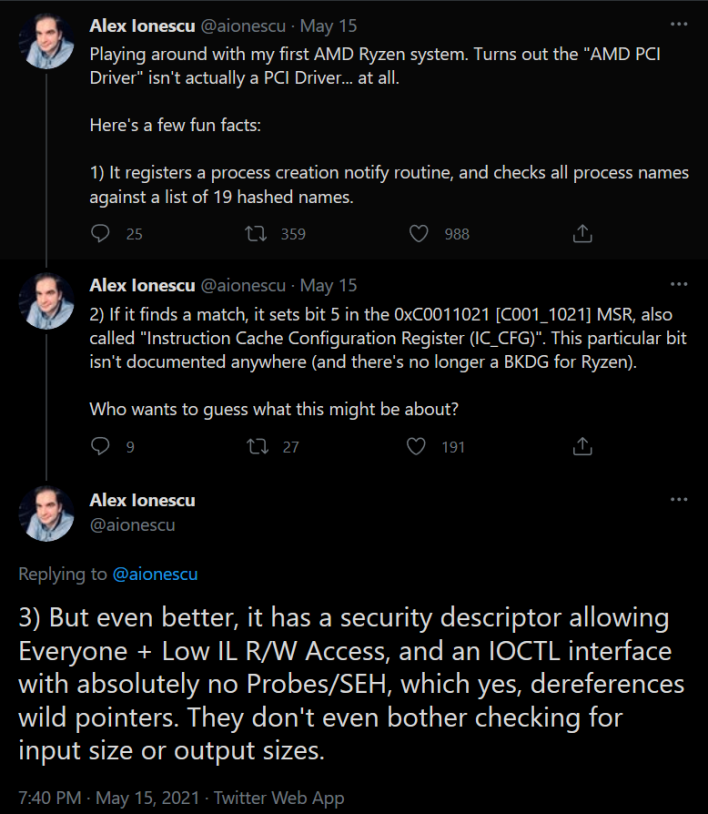
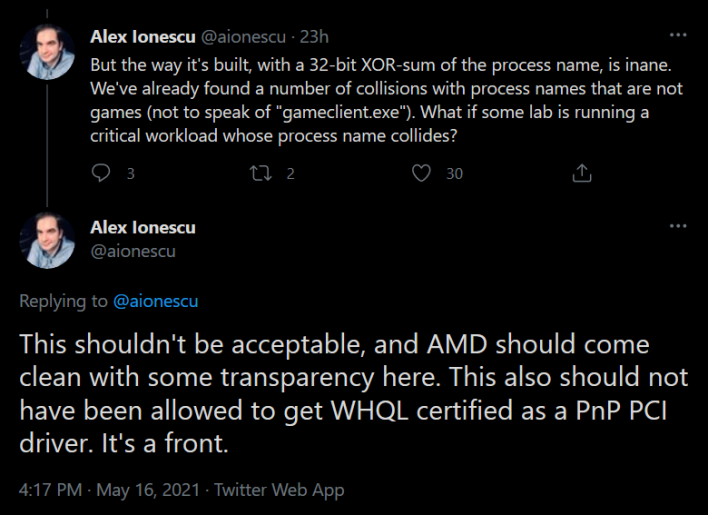
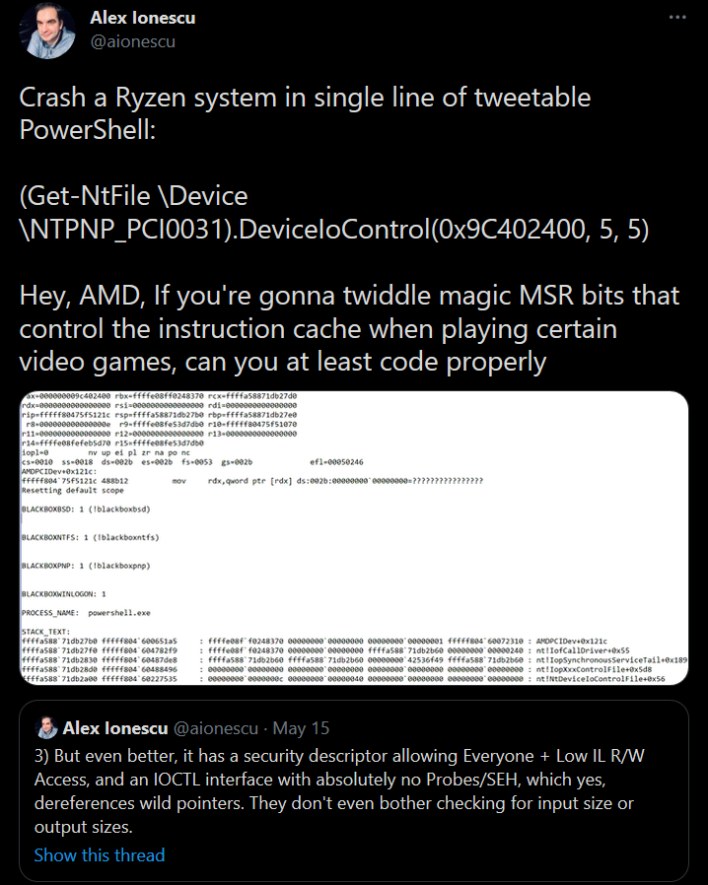
This past Saturday, security researcher and Windows Internals expert Alex Ionescu was working with an AMD Ryzen system that had a Ryzen 7 1700 under the hood. As any good researcher would do, he proceeded to dig into what was on the system and made an interesting discovery with a mysterious "AMDPciDev.sys" file. AMDPciDev.sys was WHQL certified as a PnP PCI driver, installed on the system for a "PCIe Dummy Function" device. Seeing this dummy device association, Ionescu decided to reverse engineer the driver and saw some odd behaviors like a hashing algorithm and oddities with process creation, termination, and monitoring.
Thankfully, these issues only affect stepping B1 of Zen 1 (Ryzen 1xxx) and Zen 2 XT series (Ryzen 3xxx) processors. Regardless of what this affects, as Ionescu tweeted, "the driver is vulnerable, its use is obfuscated, these checks are poorly thought out, the list of processes is arbitrary, everything is being done behind user's backs, and it affects the system globally based on a single process name."
As such, it's rather concerning that this questionable driver is apparently deployed for production-level AMD systems of this vintage. Hopefully we will find out what is really going on with this methodology being employed, as we have reached out to AMD for comment. Until we get a response, let us know what you make of this situation in the comments below.