This Innocent Lightning Cable Is A Hacker’s Dream Tap For Everything On Your Machine

The “duck test” states that if you see something and “it looks like a duck, swims like a duck, and quacks like a duck, then it probably is a duck.” However, this same logic path cannot be applied to everything, such as USB cables which could contain more than meets the eye. In the past year, a security researcher and red-team hacker nicknamed “Mischief Gadgets,” or MG for short, has developed, updated, and publicly released a family of USB cables that can be used to steal sensitive information like passwords and usernames.
Since 2008, the concept of a USB implant has existed on the Internet thanks to the NSA and a leaked project called COTTONMOUTH-I. COTTONMOUTH-I was a $20,000 USB implant that would “provide a wireless bridge into a target network as well as the ability to load exploit software onto target PCs.” As it is just a USB on the end of a keyboard, mouse, or other peripheral, it would not be suspected, therefore allowing some semblance of persistence for the malicious person or group. Since then, organizations like the NSA have likely perfected this technology, but now something similar has been made public.
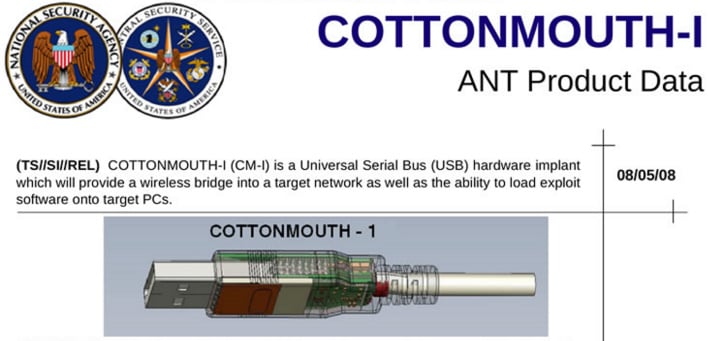
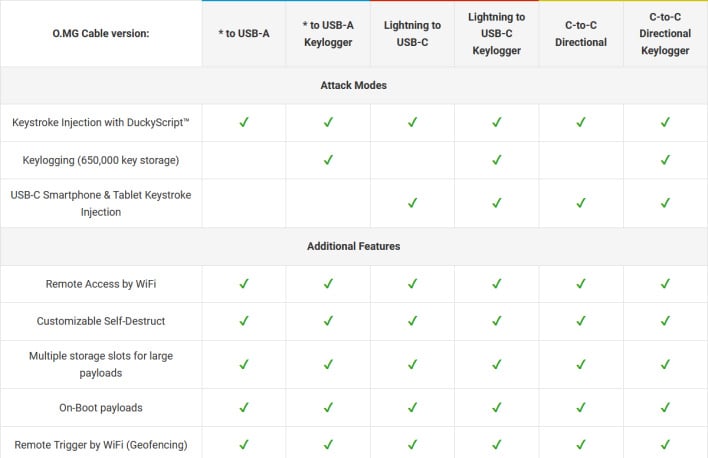

(Cottonmouth image courtesy of nsa.gov1.info. Cable comparison image courtesy of Vice.)

