Security Hazards Of The IoT: Your Printer Is A Vulnerability Minefield
Not Concerned About Your Printer's Security? You Should be
Take a look at your printer. Give it a good stare. Do you trust it? Probably not, considering it jammed the last time you had to print an important paper right up against a deadline. However, what if we told you that your printer just has to sit there on your network to be a very serious security problem?
HP Inc. recently hosted a tech field day for us, and several other security-focused journalists, at their headquarters in Palo Alto. We will speak to some of the panels we listened in on as we go, but the goal for HP at this event was to raise awareness around security - particularly where printers are concerned - and it's an important topic regardless of the brand of printing device you're using, for reasons you probably never thought of.


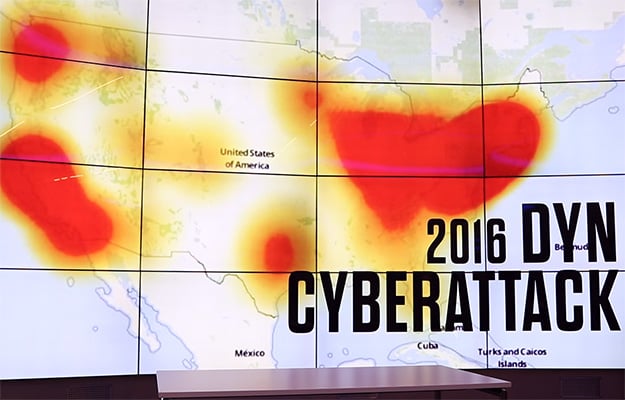
We have talked at length before about the failings of the Internet of Things. Many of these devices are developed with little-to-no concern for security. Hardcoded passwords are used. Update channels do not exist or are vulnerable to man-in-the-middle attacks. The result of all this is the rise of unparalleled botnets which can take down core internet services. The Mirai botnet infamously leverages IP cameras in its attacks, but the source code also includes plenty of ways to enslave printers.

Of course, we are not only concerned with distributed denial-of-service (DDoS) attacks, we (you) also care about the integrity of our data. A networked printer that can be enslaved for a bot army is also capable of probing the network it is on with the goal of spreading ransomware, exfiltrating confidential documents, or worse. Nothing good comes from a compromised printer and the way things exist today, the threat is all too common.

But why? Because he could. Watch his talk below for his whole story, but here’s the quick takeaway: hackers are problem solvers. Hackers view obstacles and restrictions as challenges. Hackers do not care about your CISSP certification.
“We have a serious problem on our hands,” MafiaBoy says, noting that hackers have evolved from trying to out do each other for bragging rights to becoming backed by nation-states with near unlimited resources and no legal ramifications. Ransomware schemes alone are now about a billion dollar a year industry. It is no longer enough to lock down your front door and your back door with firewalls and antivirus software. Hackers are “coming through the pipes,” he warns.

Michael "MafiaBoy" Calce
The fact of the matter is, employees are the weakest link. User awareness education can help but is seldom completely effective. MafiaBoy knows when he launches a penetration test, he can employ phishing attacks and someone, somewhere in the company will click. Once they do, an attacker can leverage any number of exploits to take control of their system and exfiltrate data. At some level, we all know this, the concept is not novel.
Well, printer code (specifically, PJL or Printer Job Language scripts) can be embedded into that document that gets executed by the printer as soon as it is sent as a print job. Recall back to the point that a modern printer is more of a computer that prints than anything else. This code can load malware onto the company printer to begin sniffing out the network all because someone checked their personal, unfiltered email on break and jumped on the offer for a free cup-o-joe. Bet you feel like "busting up a Starbucks" now, don't you. It's a bitter drink to be sure.

Let’s consider another way in. Your small office just received a fancy new networked printer. You don’t need its wireless capabilities so you just connect it via Ethernet and call it a day. The WiFi is still available and worse, unconfigured. Now an unscrupulous passerby can bridge into your network by hopping through your new printer.
Take this back another step. Right now there are servers scanning the Internet for open ports, contributing to massive databases of vulnerable targets. In their rise, printers have picked up services including the likes of FTP, Telnet, and more with these services often arriving enabled by default on new units. A few keystrokes is all it takes to search for a vulnerable printer around the world, establish a connection, and take control. Those super-confidential files your boss is printing? Someone just FTP’d a copy out from their print queue.

That's just three simple examples, and all possible thanks to the default settings most printers ship with. We could go on, but our purpose here is not to touch on every possible attack one can use to exploit a printer. Rather, like HP, also want to raise awareness that printer security needs to be taken seriously.
With that in mind, let’s explore some potential solutions, next...
HP Inc. recently hosted a tech field day for us, and several other security-focused journalists, at their headquarters in Palo Alto. We will speak to some of the panels we listened in on as we go, but the goal for HP at this event was to raise awareness around security - particularly where printers are concerned - and it's an important topic regardless of the brand of printing device you're using, for reasons you probably never thought of.

Security applies to all aspects of a network, so why is HP concerned with printers?
Many, if not most, of us are accustomed to viewing printers as a “dumb” output device: they print paper. While once true, printers are no longer tethered to a single computer waiting to accept commands, they are now standalone endpoints on the networks they're connected to. Printers are part of the Internet of Things and, like other IoT devices, employ powerful processors and run increasingly advanced operating systems. This makes them useful, it also makes them highly vulnerable, powerful attack vectors.
We have talked at length before about the failings of the Internet of Things. Many of these devices are developed with little-to-no concern for security. Hardcoded passwords are used. Update channels do not exist or are vulnerable to man-in-the-middle attacks. The result of all this is the rise of unparalleled botnets which can take down core internet services. The Mirai botnet infamously leverages IP cameras in its attacks, but the source code also includes plenty of ways to enslave printers.
Of course, we are not only concerned with distributed denial-of-service (DDoS) attacks, we (you) also care about the integrity of our data. A networked printer that can be enslaved for a bot army is also capable of probing the network it is on with the goal of spreading ransomware, exfiltrating confidential documents, or worse. Nothing good comes from a compromised printer and the way things exist today, the threat is all too common.
First, a little background
Before jumping into the specifics of printer security, we should start where HP began their panels at this event: from the mindset of a hacker. Specifically, that of Michael “MafiaBoy” Calce. MafiaBoy gained international notoriety in early 2000 by knocking Yahoo!, Amazon, E*TRADE, eBay, and other websites offline at the tender age of 15. Some estimate he caused more than a Billion US dollars in lost revenue and helped spark the Dot-Com market crash.
But why? Because he could. Watch his talk below for his whole story, but here’s the quick takeaway: hackers are problem solvers. Hackers view obstacles and restrictions as challenges. Hackers do not care about your CISSP certification.
“We have a serious problem on our hands,” MafiaBoy says, noting that hackers have evolved from trying to out do each other for bragging rights to becoming backed by nation-states with near unlimited resources and no legal ramifications. Ransomware schemes alone are now about a billion dollar a year industry. It is no longer enough to lock down your front door and your back door with firewalls and antivirus software. Hackers are “coming through the pipes,” he warns.

Michael "MafiaBoy" Calce
The fact of the matter is, employees are the weakest link. User awareness education can help but is seldom completely effective. MafiaBoy knows when he launches a penetration test, he can employ phishing attacks and someone, somewhere in the company will click. Once they do, an attacker can leverage any number of exploits to take control of their system and exfiltrate data. At some level, we all know this, the concept is not novel.
So what can go wrong? Everything, of course...
Phishing attacks are becoming increasingly clever and insidious. Imagine - to borrow an example from another HP panel - I email out a coupon for a free coffee from a certain Seattle-based chain. Even if you don’t print it out because you would not trust a strange PDF, how many of your friends, family members, and co-workers might? Worst case is the coupon doesn’t work, right? Wrong.Well, printer code (specifically, PJL or Printer Job Language scripts) can be embedded into that document that gets executed by the printer as soon as it is sent as a print job. Recall back to the point that a modern printer is more of a computer that prints than anything else. This code can load malware onto the company printer to begin sniffing out the network all because someone checked their personal, unfiltered email on break and jumped on the offer for a free cup-o-joe. Bet you feel like "busting up a Starbucks" now, don't you. It's a bitter drink to be sure.

Let’s consider another way in. Your small office just received a fancy new networked printer. You don’t need its wireless capabilities so you just connect it via Ethernet and call it a day. The WiFi is still available and worse, unconfigured. Now an unscrupulous passerby can bridge into your network by hopping through your new printer.
Take this back another step. Right now there are servers scanning the Internet for open ports, contributing to massive databases of vulnerable targets. In their rise, printers have picked up services including the likes of FTP, Telnet, and more with these services often arriving enabled by default on new units. A few keystrokes is all it takes to search for a vulnerable printer around the world, establish a connection, and take control. Those super-confidential files your boss is printing? Someone just FTP’d a copy out from their print queue.

That's just three simple examples, and all possible thanks to the default settings most printers ship with. We could go on, but our purpose here is not to touch on every possible attack one can use to exploit a printer. Rather, like HP, also want to raise awareness that printer security needs to be taken seriously.
With that in mind, let’s explore some potential solutions, next...






